AIR-CT2504-5-K9
AIR-CT2504-5-K9 Обзор
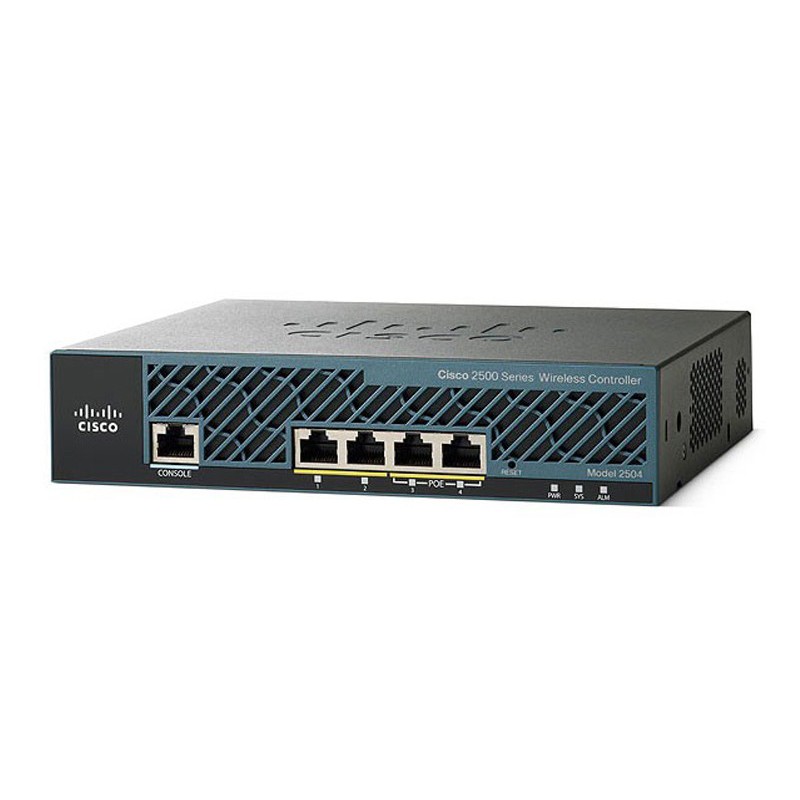
Figure 2 shows the front panel of AIR-CT2504-5-K9.
Note:
|
① |
CPU console port |
⑤ |
Power LED |
|
② |
2 GigE ports |
⑥ |
System LED |
|
③ |
2 GigE POE ports |
⑦ |
Alarm LED |
|
④ |
Reset button |
||
· Do not connect a Power over Ethernet (PoE) cable to the console port. It will damage the controller.
Table 2 shows three LEDs description.
|
LED |
Color |
Description |
|
Power LED |
Green |
Power is on |
|
Off |
No power to the system |
|
|
System LED |
Blinking Amber |
Boot-loader is active and waiting for user input from the system console. |
|
Blinking Green |
Boot-loader or booting. |
|
|
Green |
Normal System Operation. |
|
|
Amber |
System failed the bootup process or an error caused the system to halt. A status or error message is posted on the console screen. |
|
|
Off |
System not receiving power. |
|
|
Alarm LED |
Blinking Green |
Controller image upgrading. |
|
Amber |
Controller status activity, such as firmware upgrade. |
|
|
Blinking Amber |
Controller error. |
Figure 3 shows the back panel of AIR-CT2504-5-K9.
Note:
|
① |
POWER 48VDC |
② |
Cable Lock slot |
AIR-CT2504-5-K9 Specifications |
|
|
Access points |
5 licenses include (75 licenses max) |
|
Device Type |
Wireless controller |
|
Ports |
4 * 10/100/1000 ports |
|
Console ports |
10/100/1000 RJ-45 |
|
Wireless standards |
802.11a/b/g/d/e/h/k/n/r/u/w/ac |
|
Access point License |
●1 AP licese: L-LIC-CT2504-1A ●5 AP licese: L-LIC-CT2504-5A ●25 AP licese: L-LIC-CT2504-25A |
|
Security standards |
● Wi-Fi Protected Access (WPA) ● IEEE 802.11i (WPA2, RSN) ● RFC 1321 MD5 Message-Digest Algorithm ● RFC 1851 The ESP Triple DES Transform ● RFC 2104 HMAC: Keyed Hashing for Message Authentication ● RFC 2246 TLS Protocol Version 1.0 ● RFC 2401 Security Architecture for the Internet Protocol ● RFC 2403 HMAC-MD5-96 within ESP and AH ● RFC 2404 HMAC-SHA-1-96 within ESP and AH ● RFC 2405 ESP DES-CBC Cipher Algorithm with Explicit IV ● RFC 2406 IP Encapsulating Security Payload (ESP) ● RFC 2407 Interpretation for ISAKMP ● RFC 2408 ISAKMP ● RFC 2409 IKE ● RFC 2451 ESP CBC-Mode Cipher Algorithms ● RFC 3280 Internet X.509 PKI Certificate and CRL Profile ● RFC 3602 The AES-CBC Cipher Algorithm and Its Use with IPsec ● RFC 3686 Using AES Counter Mode with IPsec ESP ● RFC 4347 Datagram Transport Layer Security ● RFC 4346 TLS Protocol Version 1.1 |
|
Encryption |
● WEP and Temporal Key Integrity Protocol-Message Integrity Check (TKIP-MIC): RC4 40, 104 and 128 bits (both static and shared keys) ● Advanced Encryption Standard (AES): CBC, CCM, Counter Mode with Cipher Block Chaining Message Authentication Code Protocol (CCMP) ● DES: DES-CBC, 3DES ● Secure Sockets Layer (SSL) and Transport Layer Security (TLS): RC4 128-bit and RSA 1024- and 2048-bit ● DTLS: AES-CBC |
|
Authentication, Authorization, and Accounting (AAA) |
● IEEE 802.1X ● RFC 2548 Microsoft Vendor-Specific RADIUS Attributes ● RFC 2716 PPP EAP-TLS ● RFC 2865 RADIUS Authentication ● RFC 2866 RADIUS Accounting ● RFC 2867 RADIUS Tunnel Accounting ● RFC 3576 Dynamic Authorization Extensions to RADIUS ● RFC 3579 RADIUS Support for EAP ● RFC 3580 IEEE 802.1X RADIUS Guidelines ● RFC 3748 Extensible Authentication Protocol ● Web-based authentication ● TACACS support for management users |
|
Limitation |
● Does not support wired guest access ● Cannot be configured as an auto anchor controller. However you can configure it as a foreign controller ● Supports only multicast-multicast mode ● Does not support bandwidth contract feature ● Does not support access points in direct connect mode ● Does not support service port ● Apple Talk Bridging ● LAG ● Wired Guest |